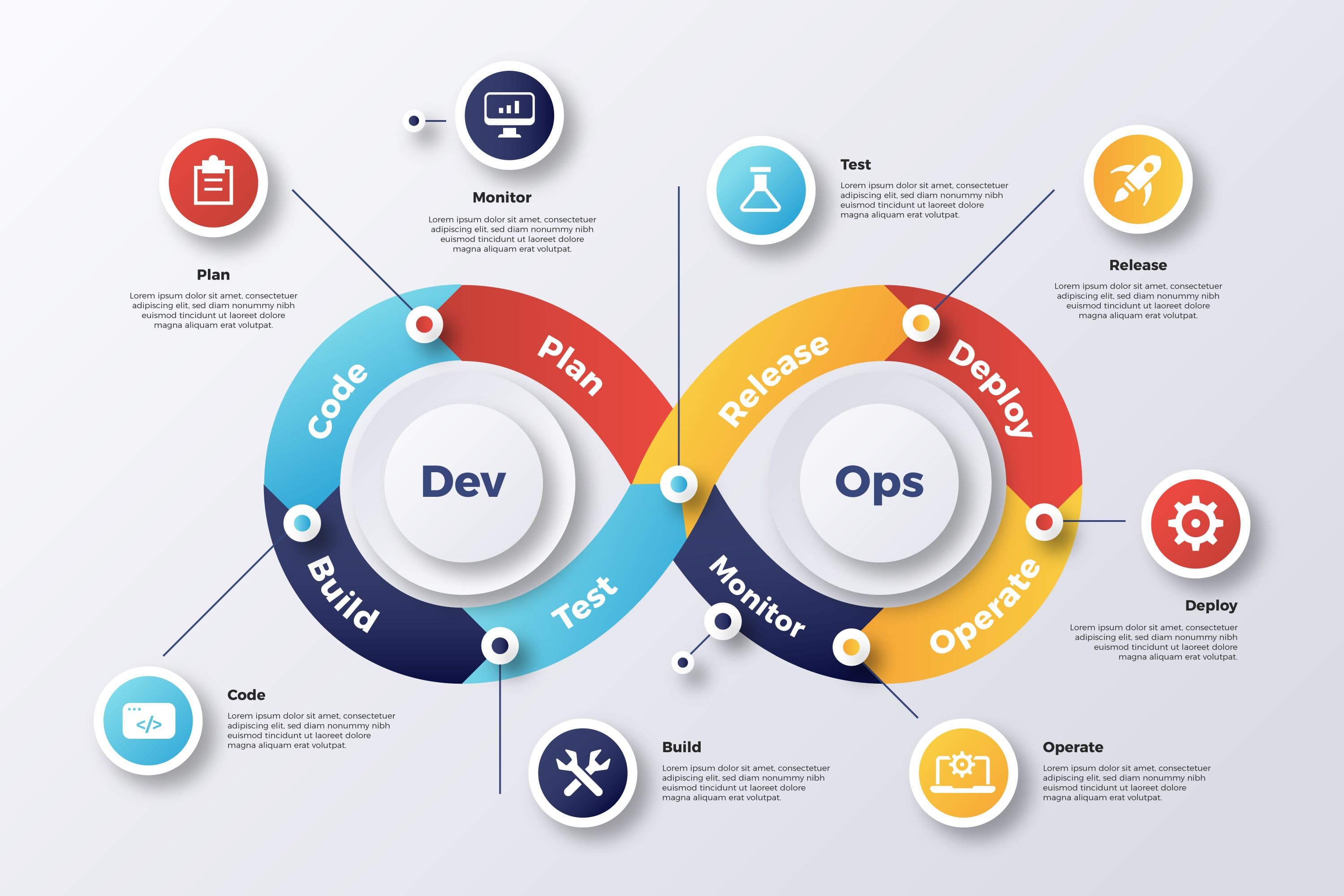

Our DevOps experts connect development and operations into a single functional unit. They ensure that new application versions can be deployed quickly and securely, infrastructure is managed efficiently, and the risk of outages is minimized. We focus on automation, scalability, and availability.
We provide experienced engineers with expertise in tools such as Docker, Kubernetes, Terraform, GitLab CI/CD, Ansible, and AWS/GCP/Azure. They have worked on projects for large e-commerce platforms, healthcare information systems, automotive backends, and public sector registries.
We can assist with CI/CD pipeline design, monitoring, infrastructure as code, containerization, and cloud migration. Our specialists integrate directly with your team and bring proven practices from real-world deployments.
| Tool / Approach | Advantages | Disadvantages |
|---|---|---|
| Docker | Fast deployment, consistency between development and production | Requires image registry management |
| Kubernetes | Orchestration, scaling, high availability | Higher complexity in setup and maintenance |
| GitLab CI/CD | Automation of builds, tests, deployments | Dependency on the GitLab environment |
| Terraform | Infrastructure as code, cloud environment management | Initial learning curve, requires versioning |
Tell us what you're working on and we’ll suggest the best approach. No strings attached – just practical advice from real experts.
Share Your Idea
Whether it’s a concept or a running project – we’ll help turn it into a technical plan.
Get Personalized Recommendations
Based on your input, we’ll recommend suitable experts or a full team based on your goals and budget.
Fast Response
We usually respond within one business day with a suggested approach or follow-up questions.